In computer science and, in particular, when talking about networks, the term door is frequently used. The doors are “access points” used by systems connected to the network to establish connections to other computers. A network connection can be made using one of the 65,535 available ports: it is then up to the operating system to associate a contact point or socket used by one or more applications to send and receive data to each port.
The netstat -na command, issued at the Windows command prompt, allows you to instantly establish which network connections are taking place or which ports are listening (“listening”) waiting to receive connection requests.
Each quadruple ( IP: port, IP: port ) indicates the source IP address (usually the IP associated with the personal computer within the local network: 192.168.xx: because in the network local are these addresses used? ), the port used on that system, the destination IP address and the port to which you connected on that computer.
The presence of the values 80 and 443, for example, suggests that you have connected to a web server using the HTTP and HTTPS protocols, respectively.
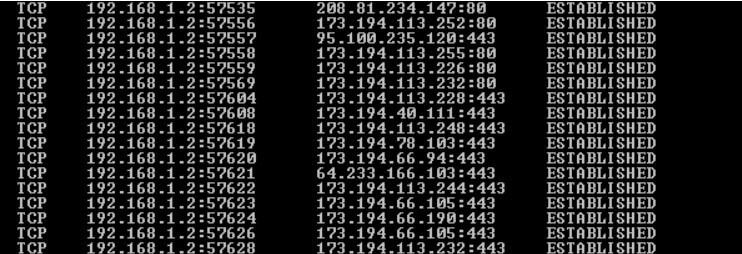
Using the netstat -fa command , the remote addresses will be automatically resolved (where possible not only the numerical IP address will be displayed).
There is no inherent danger in using specific ports. If anything, it is important to check which and how many ports are open at the entrance, accepting connections from outside.
Both when setting up a server (dedicated or cloud), and when accessing the Internet using a “consumer” router or a professional product, it is important to check open ports on the router and public IP.
If you configure a web server on your machine, it is normal to accept network traffic arriving on port 80. The important thing is that requests are handled correctly. The server does not have intrinsic vulnerabilities, which must always be prompt via the” application of security patches released by various software manufacturers.
When installing a server component that needs to listen (“listening”) to the incoming connection requests, you need to make on the so-called router port forwarding or port forwarding. In other words, the router must forward all the traffic arriving on a specific port, on the interface associated with the public IP, to the system connected to the local network where the server component is running.
By activating port forwarding on the router, the server component installed on the machine connected to the local network will no longer respond only to connection requests from the LAN but also to those arriving from the “outside world” (Internet network).
We have seen how to open ports on the router, forward data packets, and close ports that are no longer needed.
How many ports are there and Images
We have already highlighted how the communication ports follow a 16-bit numbering (altogether, that is, 65,535 equal to 2 16 -1).
The first 1,024 ports (called “well-known ports”) are associated with specific services, some of which are well known, provided by the IANA ( Internet Assigned Numbers Authority ), a body, a department of the well-known ICANN, which is responsible for assigning IP addresses.
Therefore, among the first 1,024 ports, just remember that, by convention, the 20 and 21 are used, for example, by the FTP protocol for file transfer; 25 and 465 from the SMTP protocol (465 over SSL); 80 from HTTP; the 110 and 995 from POP3 (the 995 on SSL); 443 from HTTPS; 53 from DNS; le 137-138-139 from NetBIOS and so on.
A complete list is available at this address on the IANA website. A more readable “commented” list is then available here on Wikipedia.
Starting from the port number listening on a system or open on the public IP on which the router is connected, it is, therefore, possible to know immediately what type of service is running.
Also, as a precaution, it is important to check the open ports on routers and public IPs. Attackers and cybercriminals often scan large IP addresses for open ports on which vulnerable services are attested.
You can think, first of all, resort to the famously free service from Steve Gibson Shields Up!
GRC Shields Up!
To use Shields Up! and check the open ports on the router and public IP, you can connect with this page and click on Proceed.
When the next page appears, click on All service ports. In this way, the service will sequentially check the first 1,056 ports by examining the public IP address you are presented with.
The “invisible” ( stealth ) doors are highlighted in green, in red those “open” (therefore reachable remotely), in blue those visible even if closed.
If server functions have been activated, it is good to check that only the ports associated with services you want to make accessible from the outside are open. In the case of a router used in a company or office, port 80 should be, for example, normally closed (indeed, indicated as “invisible”), unless port forwarding has been carried out to a server system, connected to the local network, to which one must be able to connect – after entering the access credentials – from the outside.
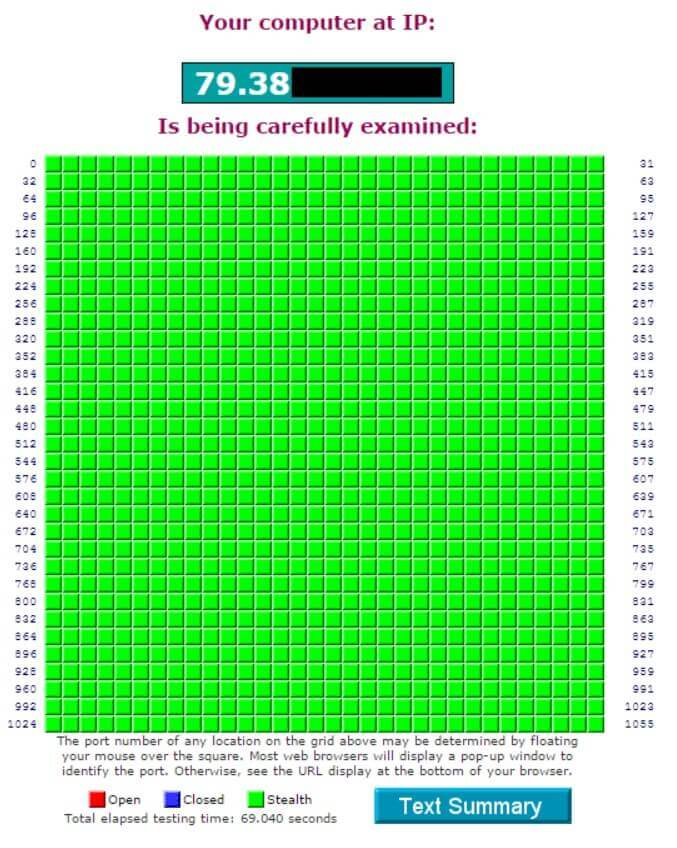
Shields Up! allows you to scan your IP only. In other words, it is not possible to examine remote IP addresses belonging to third parties.
YouGetSignal
Also, YouGetSignal allows, like Shields Up !, to control the open ports on the router or the public IP. By pointing the browser at this page, you can specify which port should be checked while clicking on the scan all common ports link; YouGetSignal will check the most commonly used ports.
The service makes no difference between closed doors and invisible doors: the doors are indicated either as open or simply as closed.
However, it is also possible to scan public IPs other than the one in use, even if YouGetSignal allows you to examine one port at a time.
T1 Shopper
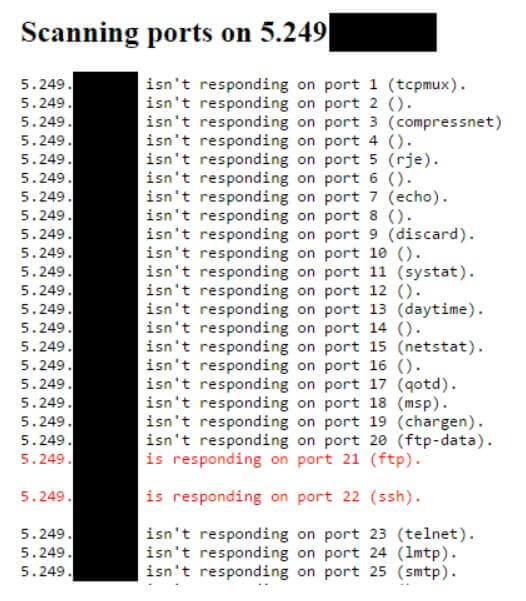
The free tool for scanning open ports accessible from this page allows you to check the open ports on any IP address, not only the public IP you are presented with.
By default, the public IP address you are currently connected to the network appears in the Hostname or IPv4 address field.
It is, however, possible to change this address by specifying any other IP address to be examined.
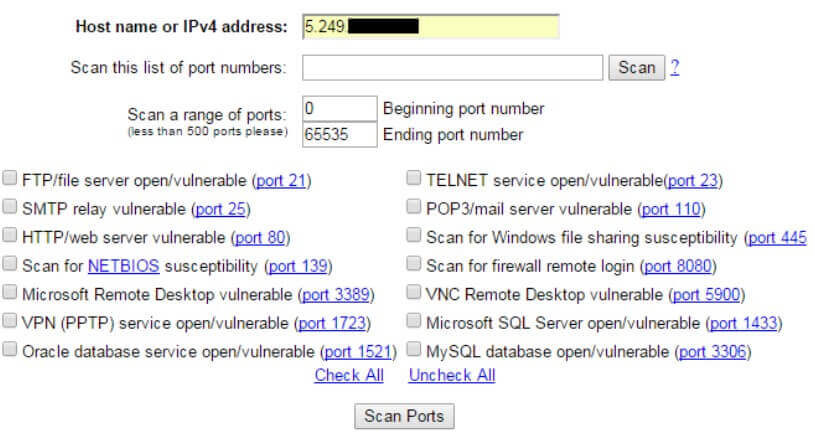
By clicking on Check all and then on the Scan button, you can limit the scan to the 14 indicated ports.
Using the scan this list of ports numbers and Scan a range of ports boxes, you can request a scan of a set of specific ports instead.
The service will perform the scan in real-time, indicating gradually which ports are open, which are closed, and which do not provide any type of response (the request “falls on deaf ears”).
MX Toolbox
Another alternative service is MX Toolbox. By connecting with this page, you can access a variety of tools that not only allow you to check open ports on any public IP but also control the DNS server configuration, do a WHOIS (to determine who has headed a domain), PING and Traceroute, check host reputation and any blacklisting, check any SPF antispam records and much more.
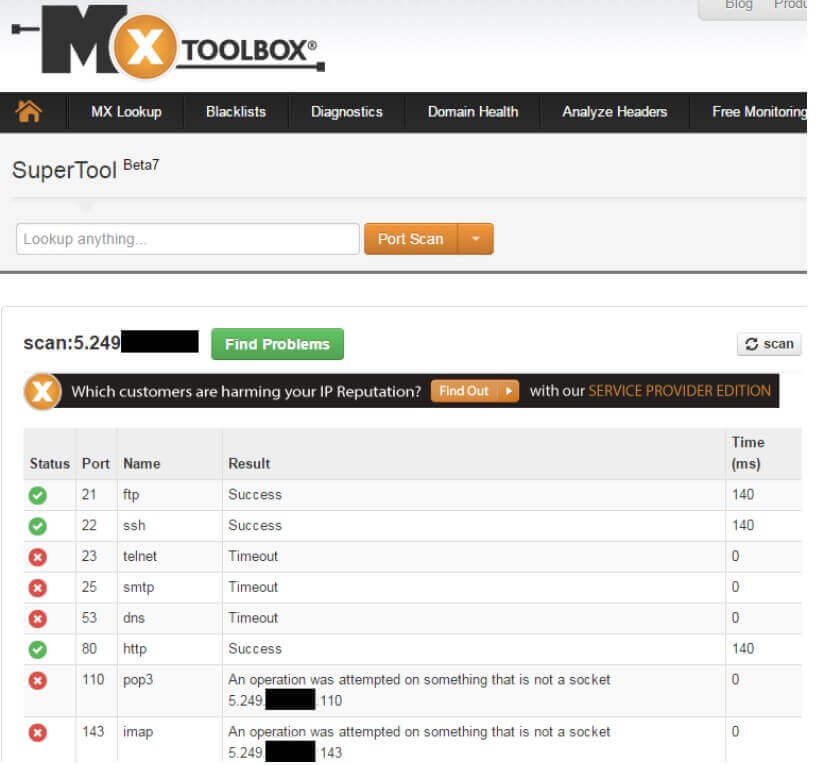
To start a port scan, simply type scan: in the Look anything field, followed by the IP to be scanned. MX Toolbox, however, limits the scan to the most commonly used ports.
A tech-savvy writer with a knack for finding the latest technology in the market, this is what describes John Carter. With more than 8 years of experience as a journalist, John graduated as an engineer and ventured soon into the world of online journalism. His interest includes gadget reviews, decoding OS errors, hunting information on the latest technology, and so on.