Despite the changes recently applied to Windows 10 and the operation of Windows Defender, it is still possible to reset the password of user accounts and create new accounts with administrative privileges by the installation media of the operating system.
Update: We have released a new version of the batch file (August 2020). It automates the deactivation of Windows Defender tamper protection to create a new account or manage existing ones if you do not remember the corresponding password.
The content of Windows systems that do not use full drive encryption (hard disk or SSD) is easily accessible by third parties, unauthorized users, or outright malicious individuals. If the drive is not encrypted with Bitlocker or VeraCrypt, use a simple boot media (Windows PE, a Linux distribution, or even the simple Windows installation media) to access the contents of files and folders without limitations, with the ability to copy the material elsewhere (e.g. to removable media or a network location).
With this article, we want to demonstrate that anyone with physical access to a Windows 10 system, updated to the latest version ( Windows 10 May 2020 Update, version 2004included), can even create new users with administrative privileges and change the password of the various accounts present unless the user has not activated Bitlocker or similar tools.
A trick that allows you to access the Windows 10 system in case of a forgotten password
Many know the trick that until some builds of Windows 10 are allowed to add and activate a new administrator account and change the user accounts’ passwords (by logging in as another person quietly).
The expedient was based on using some system tools for accessibility or designed and developed to improve the experience of using Windows devices by disabling it.
Therefore, using the Windows 10 recovery console or the operating system installation media, you can reset the password of any account by renaming the system file \ windows \ system32 \ sethc.exe in \ windows \ system32 \ sethc .old and copying the command prompt in its place (copy c: \ windows \ system32 \ cmd.exe c: \ windows \ system32 \ sethc.exe).
Till now, you can force the command prompt’s appearance with administrative rights by restarting the machine and pressing the SHIFT key five times in a row when the Windows 10 logon screen appeared.
Since Microsoft had introduced some changes to the behavior of Windows Defender, the “trick” no longer worked.
Trying to put it into practice, pressing the Windows + R key combination on the Windows desktop and then typing sethc.exe , the error message ” The operation cannot be completed. The file contains a virus or potentially unwanted software ” will appear. At the same time, Windows Defender (double-clicking on its icon in the tray bar then on View Threat Details, Show Full History ) will expose the message “(Serious) Trojan: Win32 / Accessibility.Escalation.A “referring to the file \ windows \ system32 \ sethc.exe.
To confirm how important it is today to encrypt the entire drive with Bitlocker or similar solutions, we are managed to pass the checks recently imposed in Windows 10.
In this way, it is possible to remove the password of other accounts, reset the password of any user account and create new accounts in Windows 10 by forcing the command prompt’s appearance at the logon screen. Here are the steps we used:
1) Insert the Windows 10 installation media into a USB key. To do this, go to this page, click on Download the tool now, and then prepare a bootable USB key with the Windows 10 installation files.
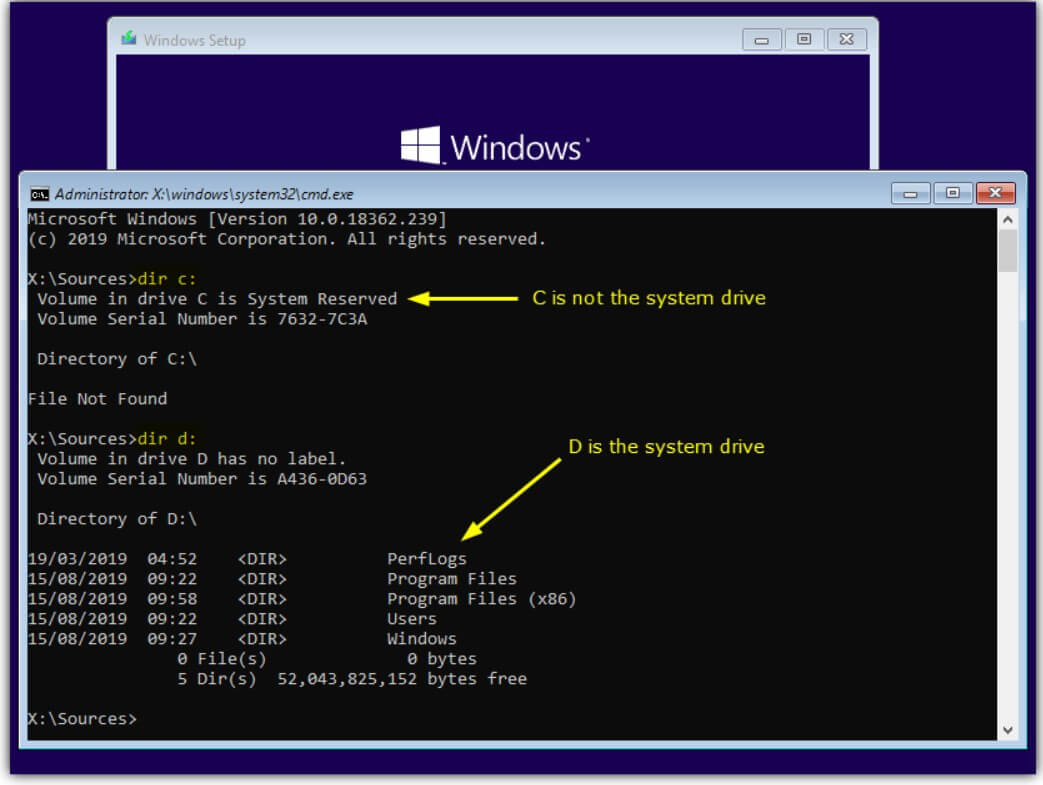
2) Boot the system from that media.
3) When the screen for choosing the language and keyboard layout appears, press SHIFT + F10 so that the command prompt appears.
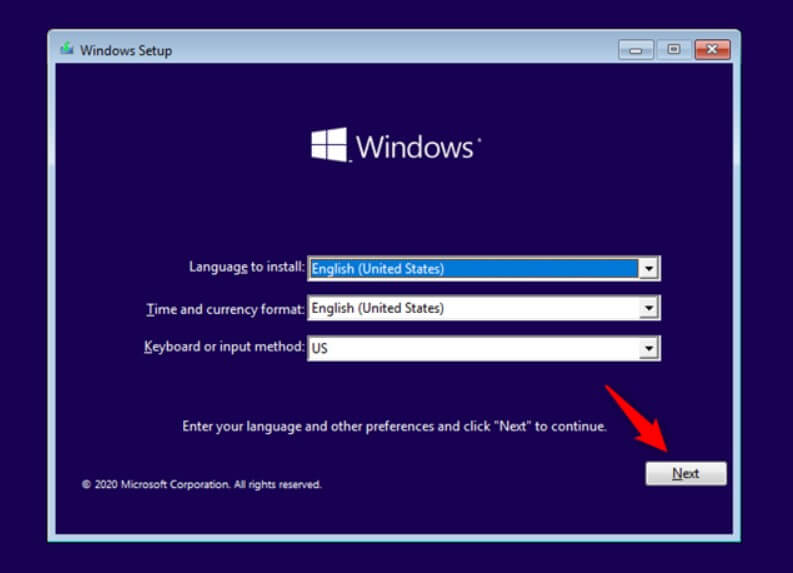
4) Check the drive where Windows 10 is installed. In this environment, this may not necessarily be the C: drive. For example, type dir C: \ windows and then dir D: \ windows or dir E: \ windows until you find the correct drive letter.
5) Now, type Regedit, click on the HKEY_LOCAL_MACHINE branch, choose the File menu, Load hive, and then type D: \ windows \ system32 \ config \ SOFTWARE in the File name box.
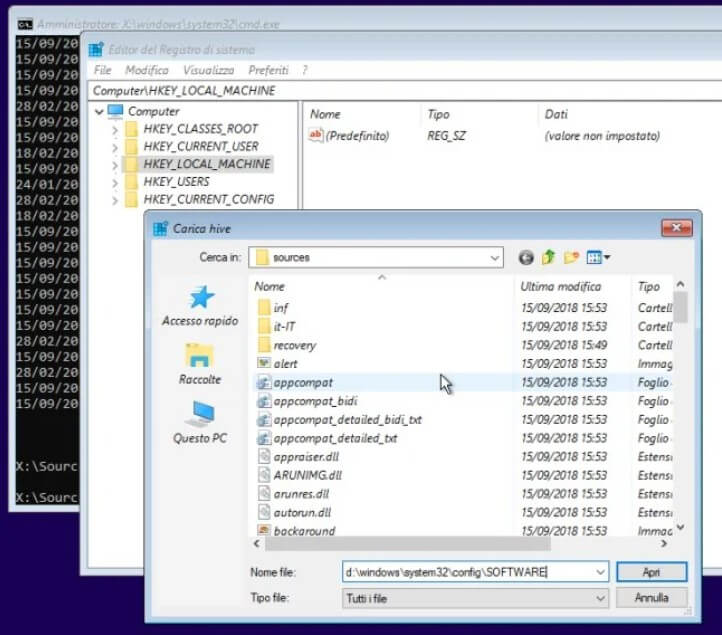
6) After clicking the Open button, Registry Editor will ask you to enter a name for the key you are uploading. We suggest entering WINDOWS10.
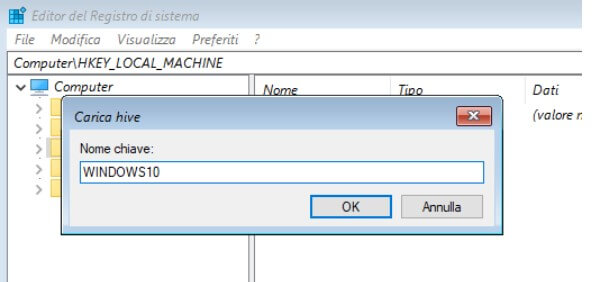
This will give you access to the contents of the HKEY_LOCAL_MACHINE \ SOFTWARE key of your Windows 10 installation.
7) Click on the HKEY_LOCAL_MACHINE \ WINDOWS10 branch.
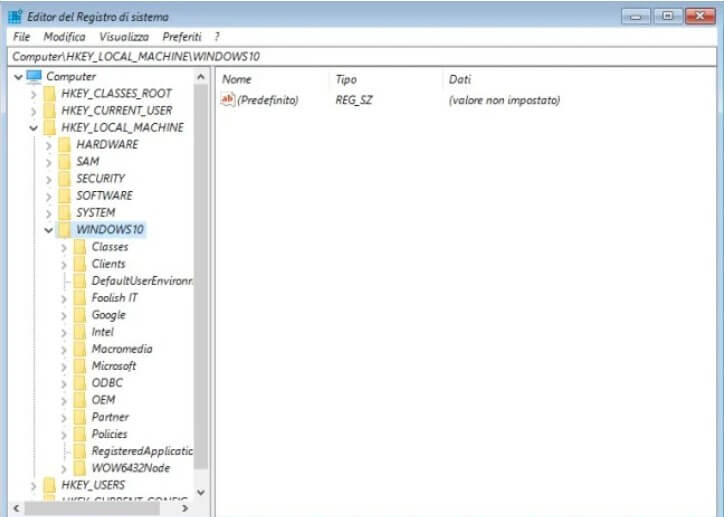
8) Go to the HKEY_LOCAL_MACHINE \ WINDOWS10 \ Policies \ Microsoft \ Windows Defender key then, in the right panel, right-click, select New, DWORD value (32 bit) assigning it the name DisableAntiSpyware and the value 1.
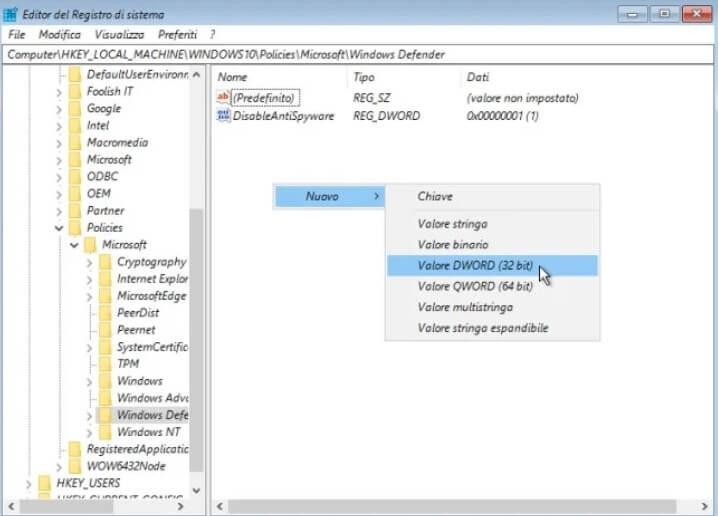
You are doing so to temporarily disabled Windows Defender on your Windows 10 installation.
9) Go to the HKEY_LOCAL_MACHINE \ WINDOWS10 \ Microsoft \ Windows NT \ CurrentVersion \ Image File Execution Options key.
Then right-click on Image File Execution Options and choose New, Key.
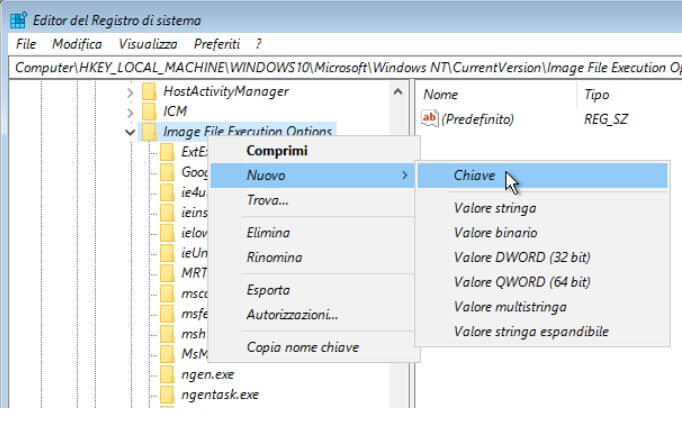
Give the new subkey just inserted the name sethc.exe .
10) Select the key HKEY_LOCAL_MACHINE \ WINDOWS10 \ Microsoft \ Windows NT \ CurrentVersion \ Image File Execution Options \ sethc.exe , click in the right panel and then select New, String value.
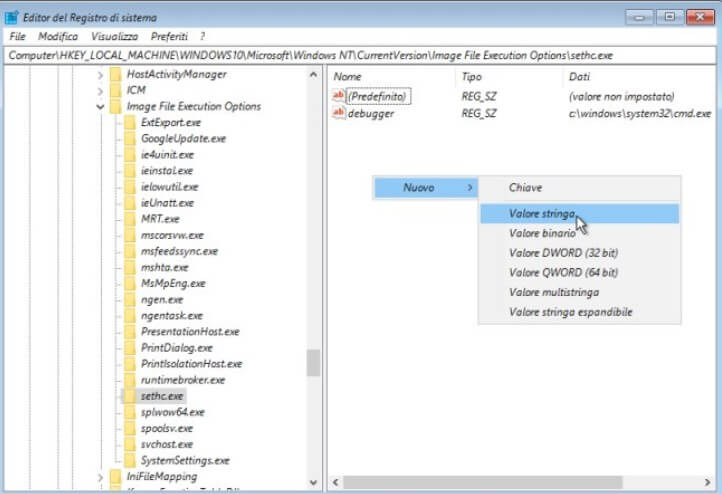
11) Assign the named debugger to the string value just added and c: \ windows \ system32 \ cmd.exe as value.
12) Go to the HKEY_LOCAL_MACHINE \ WINDOWS10 \ Microsoft \ Windows Defender \ Features crucial and then change the TamperProtection DWORD value to 0.
13) Press the “X” of the various open windows repeatedly to restart the machine and extract the media containing the Windows installation files.
14) When the Windows 10 logon window appears, by pressing the SHIFT key five times consecutively, the command prompt window will appear.
From here, by typing the following, you can create a new administrative account:
net user test admin / add
net localgroup administrators testadmin / add
With the command net user testadmin *, you can set a password.
The same command, specifying instead of testadmin the name of an account present on the machine, will allow you to reset any other version’s password: Windows 10 will ask for the new password to be set.
To undo the changes you made previously, you can login to Windows 10 with an account with administrator privileges, type cmd in the search box, and then press CTRL + SHIFT + ENTER.
Then type:
reg delete “HKLM \ SOFTWARE \ Microsoft \ Windows NT \ CurrentVersion \ Image File Execution Options \ sethc.exe”
reg delete “HKLM \ SOFTWARE \ Policies \ Microsoft \ Windows Defender” / v DisableAntiSpyware
reg add “HKLM \ SOFTWARE \ Microsoft \ Windows Defender \ Features “/ v TamperProtection / t REG_DWORD / d 1 / f
Once you have forgotten the password of a Windows user account, even an administrative one, the procedure illustrated in our article is beneficial.
Important: The interventions indicated above do not work if the accessibility keys were disabled on the Windows 10 system in use (manually or via script), i.e. by pressing the SHIFT key for at least five times consecutively, the function of the operating system that usually determines the appearance of the window shown in the figure.
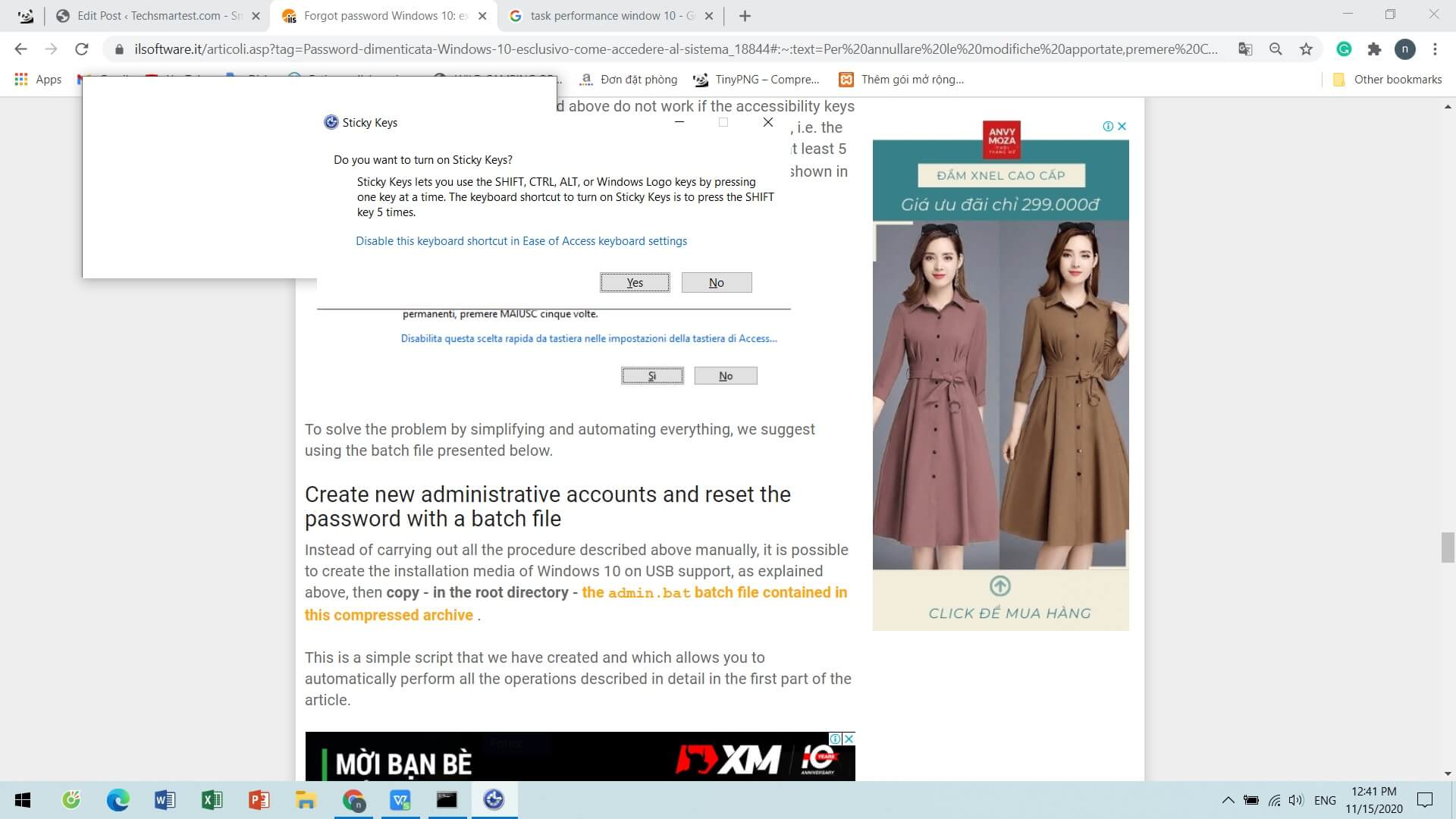
To solve the problem by simplifying and automating everything, we suggest using the batch file presented below.
Create new administrative accounts and reset the password with a batch file
Instead of carrying out all the procedures described above manually, it is possible to create the installation media of Windows 10 on USB support, as explained above, then copy – in the root directory – the admin.bat batch file contained in this compressed archive.
This is a simple script that we have created and allows you to automatically perform all the operations described in detail in the first part of the article.
After booting the system from the Windows 10 installation media, when the screen for choosing the language and keyboard layout appears, you have to press SHIFT + F10 and then move from the X: \ Sources folder to the drive containing the root folder of the ‘USB drive (usually from D: onwards).
For example, you can type dir D: \ admin.bat or dir E: \ admin.bat or dir F: \ admin.bat until you find the correct drive letter.
At this point, you can type this letter found previously (for example, D :, E :, F: or others) and press Enter.
Writing admin at the command prompt, and then press Enter in a batch will change the configuration of the first installation of Windows 10 on the hard disk or SSD. By restarting the machine and pressing the SHIFT key five times when the login window appears, you can change the passwords of existing accounts or create a new tab with administrative rights (see the net user commands presented above).
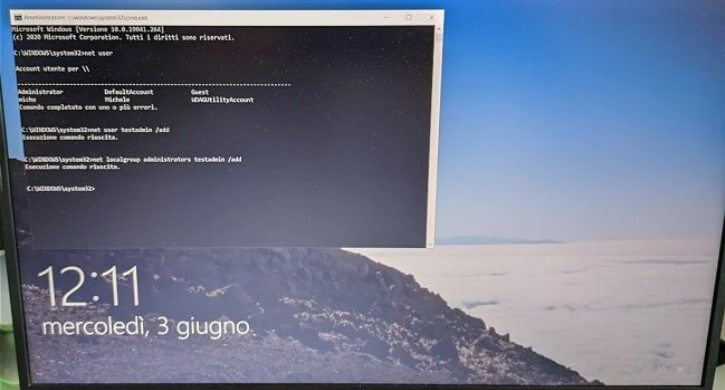
As you can see in the image, we have created a new testadmin account giving it administrative rights in our case. This account, once completed, will become immediately accessible.
If you don’t see it appear in the Windows 10 logon screen’s lower-left corner, restart the operating system.
If, as in the example, no password has been assigned to the newly added administrator account (command net user testadmin * ), Windows 10 will automatically log in to this account at each subsequent restart. To log out of this account, press the ALT + F4 key combination and then choose the Change user item.
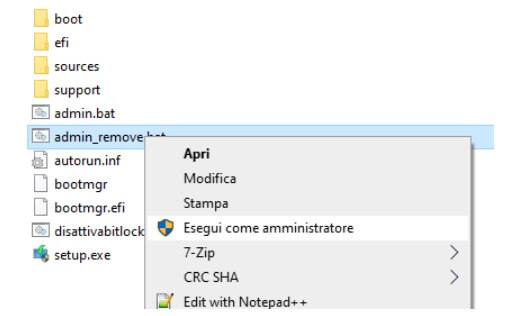
After logging in, usually in Windows 10 with any account, to cancel the changes, use the admin_remove.bat file by clicking on it with the right mouse button and choosing Run as administrator .
An alternative solution: NTPWEdit
Based on the well-known chntpw tool, the NTPWEdit utility allows you to change any account’s password using a different approach. The program does not decrypt the password but allows boot to modify the contents of the \ WINDOWS \ SYSTEM32 \ CONFIG \ SAM file, which contains the user accounts’ credentials in use.
To change the forgotten password of a Windows account, just:
1) Create the ntpwedit folder in the root directory of the Windows 10 installation media created using USB media.
2) Save the contents of this compressed file in this folder.
3) Reboot the system from the USB media thus configured.
4) On the screen that allows you to choose the language and keyboard layout, press the critical combination SHIFT + F10.
5) Move from the X: \ Sources folder to the drive containing the USB drive’s root folder (usually from D: onwards).
For example, you can type dir D: \ ntpwedit either dir E: \ ntpwedit or dir F: \ ntpwedit until the correct drive letter is found.
6) Type this letter (for example, D :, E :, F: or others) and press Enter.
7) Write cd ntpwedit and then ntpwedit64 .
8) When the main window of NTPWEdit appears, make sure that the correct path is shown in the Path to SAM file box, then click on Open.
9) By selecting one of the Windows user accounts and clicking on Change password, you can choose and set a new password.
10) As a final step, remember to click the Save changes button. By clicking on Exit and then on the “X” of the various windows, you can restart the system.
What is illustrated in the article highlights how it is now essential to encrypt the content of the entire unit. In this regard, we suggest reading our following articles:
– BitLocker, what it is, how it works and why it should be activated from a GDPR perspective
– BitLocker, how key recovery works and unlocking with USB
A tech-savvy writer with a knack for finding the latest technology in the market, this is what describes John Carter. With more than 8 years of experience as a journalist, John graduated as an engineer and ventured soon into the world of online journalism. His interest includes gadget reviews, decoding OS errors, hunting information on the latest technology, and so on.