MAC Address is the special unique identifier that each hardware manufacturer assigns to every network card, ethernet and wireless, placed on the market. The MAC address is 48 bits (6 bytes) long, and the first three octets identify the organization or company that created the communication interface. The first part of each MAC address always has one of the prefixes (” Organizationally Unique Identifier ” or OUI) indicated in this text file, a document that is constantly updated by the IEEE (the international association of professional scientists whose objective is the promotion of technological sciences).
The MAC address can indeed be changed via software; nevertheless, it can be considered as a parameter that, in general, allows to identify a device uniquely.
A system equipped with multiple network cards will use several MAC addresses that are different from each other: in the case of a notebook, for example, one MAC Address is associated with the Ethernet interface while the other with the wireless one. Any USB Wi-Fi key, which can be used to allow a computer without a wireless card to connect to a wireless network, also uses its own MAC address.
Since the total 48-bit MAC addresses that can be assigned are 248 or more than 281.4 trillion, the IEEE expects to run out of them around 2100. MAC addresses are composed of 64 bits (EUI-64), which, are much more numerous and are used on Firewire cards and IPv6 networks.
All routers available on the market usually offer the possibility of carrying out an additional check regarding the wireless connection, checking the MAC address of each client system attempting the connection. By entering, in a specific section of the wireless router configuration panel, the list of MAC addresses of the systems entitled to access the network, the router will also carry out this additional check. It is an extra security measure, but its presence must be remembered whenever you want to connect a new wireless device to the network. If you do not add the right MAC address in the Wi-Fi router’s administration panel, the new wireless device will not be able to connect even if you set the correct password.
However, it must be said that protecting the wireless network using only MAC address filtering is certainly not the best choice. It would be like putting a security officer at the door of a room who checks the one eligible for entry based on what is written on a plate affixed to the jacket. The tag can be fake, and an “attacker,” determined to enter, may have previously read what is written on others’ tags.
A good security strategy, however, must always rest on multiple levels in its own right. Ensuring you are using a secure cryptographic algorithm for securing your Wi-Fi network (at least WPA2) is the first thing to do. Equally important is the choice of sufficiently long and complex password protection. Only as an additional defence layer will it be possible to think about enabling the MAC address check.
Anyone determined to access your Wi-Fi network will try to use a tool like Aircrack-ng to find out the password used. In the case of the WEP algorithm, the keyword is extracted immediately, without any effort. In the case of WPA, the procedure may not take long, especially in short and not particularly complex passwords (see the article Cloud computing again used for attacks against WPA and the previous WPA cryptographic protocol attack presented ).
The WPA2 algorithm remains today, however, an excellent choice, especially if you take care to set a sufficiently long and complex password.
A good tool for checking the intrinsic security of a wireless network is Cloud Cracker. This is a paid service that requires, at the input, a log file containing the handshake packets previously captured with software such as Aircrack-ng. The site will analyze the transmitted file by starting a sort of brute-force attack that takes advantage of the enormous computing power offered: it is possible to use hundreds of CPUs simultaneously to divide the workload and speed up the “recovery” of the Wi-Fi password. For each “job,” Cloud Cracker indicates the time needed to trace the password used to protect the wireless network and the price required to complete the assigned task. The user can decide whether to proceed, paying the indicated amount, or to cancel the operation.
The MAC address of the network card is often printed on the label physically applied to the hardware, or it can be deduced, in a Windows environment, by opening the command prompt window (Start, Run …, cmd ) and typing the following: IPCONFIG / all. Therefore, it will be necessary to carefully analyze the output obtained and note the ” physical address ” indicated under ” Wireless LAN card Connection to the wireless network “.
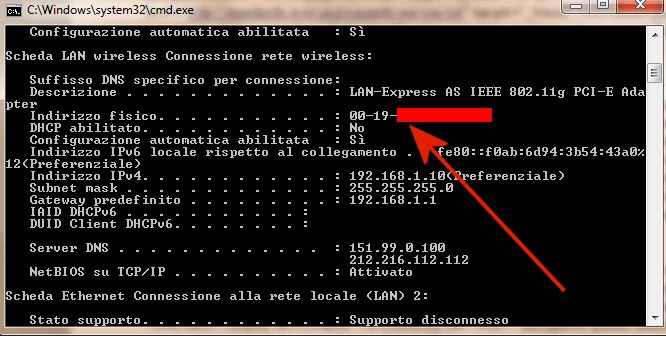
This MAC address, consisting of six pairs of digits, can be entered in the router administration panel in the Wireless access or MAC address access-list section if you also want to enable MAC filtering.
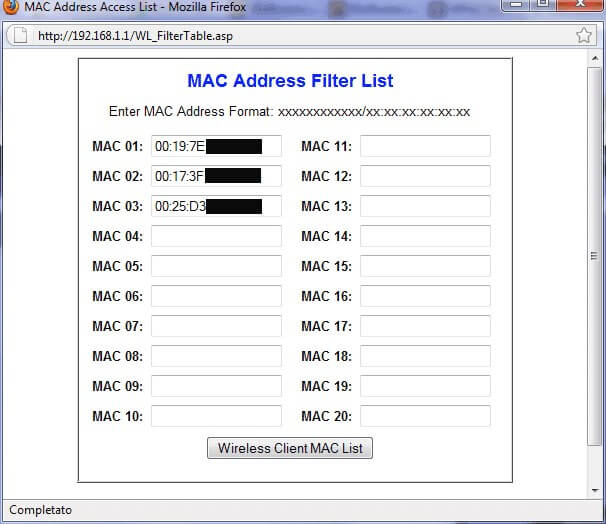
For example, the following setting (the interface is that of a Linksys router) allows you to activate the filter on the MAC address ( Restrict access ) and to allow access to the Wi-Fi network only to the explicitly indicated addresses ( Permit only ).
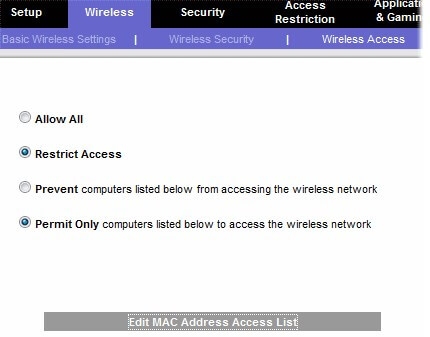
To specify the MAC addresses associated with the authorized client systems, in this case, it is necessary to click on the Edit MAC address access-list and then type them, one after the other, in the appropriate boxes. Looking at this document, you can see that the first card is produced by Hon Hai Precision, the second by Belkin, and the third by AzureWave.
In Linux, to retrieve the MAC address, simply open a terminal window and then type the command ifconfig-a checking what is displayed in correspondence with the indication HWaddr, next to the entry relating to the wireless interface (often referred to as ” wlan0 “).
On Mac OS X systems, just access the System Preferences … window, click on the Network icon, select the wireless interface, and click on the Advanced button. The MAC address will be shown in the window that will appear on the screen.
The MAC address of any mobile device can be extracted simply by accessing the device settings. In the case of an Android smartphone or tablet, for example, just “tap” on Info on the device, on Status, and then scroll down to locate the item Wi-Fi MAC address (the Wi-Fi connection must be active).
A tech-savvy writer with a knack for finding the latest technology in the market, this is what describes John Carter. With more than 8 years of experience as a journalist, John graduated as an engineer and ventured soon into the world of online journalism. His interest includes gadget reviews, decoding OS errors, hunting information on the latest technology, and so on.