Not just a guide to setting up Google DNS: an in-depth study to understand how they work and what’s behind it.
When you surf the net and type in any mnemonic address such as www Q.software, it in the browser, the request passes (almost; we will see later why) always through a DNS server ( Domain Name System ) which resolves the domain and determine which IP address (IPv4 and/or IPv6) it matches. Any other application installed on the system – therefore not necessarily the web browser – that uses not the IP address but a mnemonic address to connect to a remote server will also send the request for resolution of the domain name through a DNS.
How Google DNS works and what it is for
Each system connected to the Internet is identified with a unique public IP address; a mnemonic address can point to one or more IP addresses.
Like all other DNS used at the global level, the Google DNS is concerned with resolving domain names.
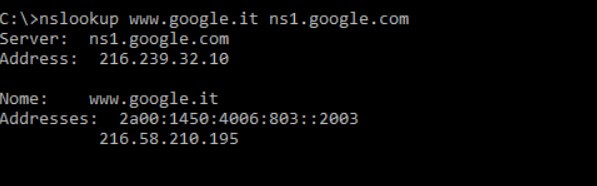
In Windows, try opening the command prompt using the Windows + R key combination then typing cmd. In Linux, open the terminal window. At the prompt, type the following: nslookup www.google.it
The DNS server used will provide the public IP addresses associated with the mnemonic address www.google.it (the first, in this case, is an IPv6 address while the second is the traditional IPv4):
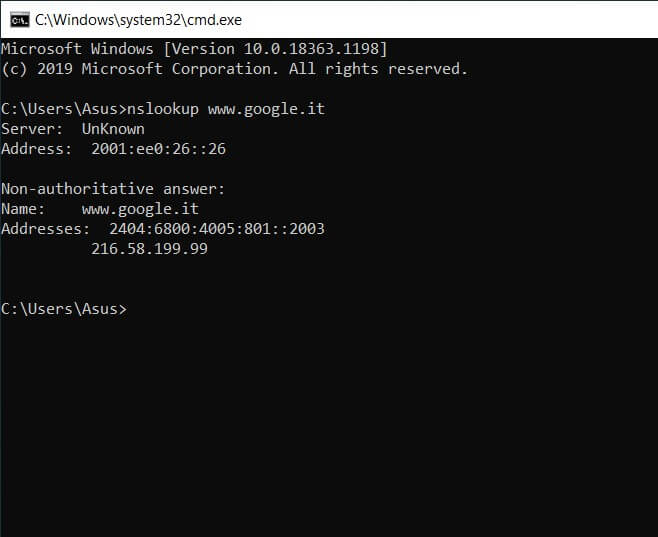
The nslookup command, regardless of the operating system, will also indicate the DNS server that was queried to get the correct destination IP address or IP addresses.
By copying the IPv4 address in the browser’s address bar, the Google server will handle the request and – as you can easily verify – will automatically redirect to the search engine home page.
How does the resolution of domain names thanks to DNS
Whenever you type a mnemonic address in the browser’s address bar, first the content of the local system’s HOSTS file is checked ( Edit the Windows HOSTS file and block the apps that “call home” ) then switch to the resolver cache Operating system DNS (can be flushed from a prompt, in Windows environment, using the ipconfig / flushdns command; see DNS server not responding: how to fix ).
In this way, it is ascertained whether the IP address of the destination Internet site is already known locally or, in any case, set manually by the user (this is the case of the HOSTS file).
If the correspondence between the IP address is not known locally, the system queries the user’s DNS server (in the network interface settings or at the modem router / DHCP server level). If the requested DNS server does not know the IP corresponding to the domain name indicated, then the so-called recursion mechanism is activated: you start from the root by querying one of the root servers in the top-level domain, you get the ServerServer that manages it, proceed to a query in the second level domain until the authoritative ServerServer for the desired name is reached.
Google DNS: why it is needed and what alternative DNS is
Usually, users, especially those who use the modem router provided by the Italian telecommunications operator, use – without knowing it – the DNS server provided by the same provider.
These are communicated by the modem router to all devices connected in the local network via Ethernet cable or WiFi using a DHCP protocol.
The Google DNS, as indeed many others may be regarded as alternative DNS and are among the fastest DNS server.
Use an alternate DNS server(those of the Mountain View company are also known as Google Public DNS because they can be used publicly or used by any user on the face of the earth, with any device and any connection ) it several advantages.
Changing DNS and choosing, for example, Google’s allows, first of all, to browse online without censorship.
Some websites whose access has been blocked at the local DNS level by Italian providers are instead regularly accessible by machines that rely on Google DNS, OpenDNS, Cloudflare, etc.
In the case of sites blocked at the level of the Italian DNS, in fact, instead of the real IP, 127.0.0.1 is obtained in the Response provided by the nslookup command. Thus, neither the browser nor other applications can reach the servers corresponding to the specified mnemonic address.
The network structure on which Google’s DNS servers or Cloudflare’s DNS servers are based allows a faster resolution of domain names while in the case of OpenDNS it is even possible, as mentioned above, to activate filters so that you can block or allow the visit of individual websites.
The Google DNS allows minimizing the latencies between the request for the resolution of a domain and its IP sending to the client. The coverage of Google DNS servers is almost global to physically place a nameserver as close as possible to the user who requests it.
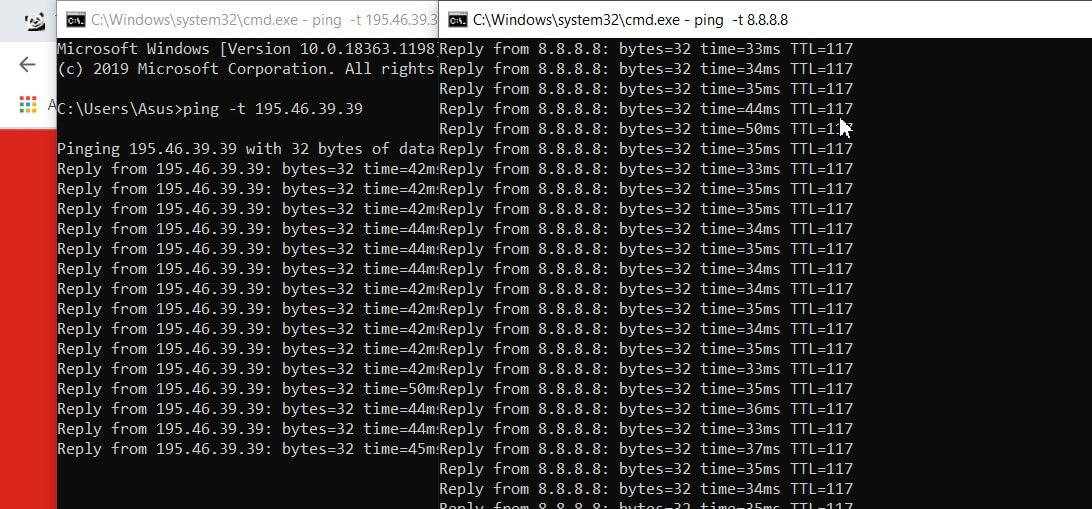
Look at the following ICMP requests (pings): reaching the Google DNS servers adds just 4-5 ms to the Response of the first hop of the network connection in use (in this case, TIM).
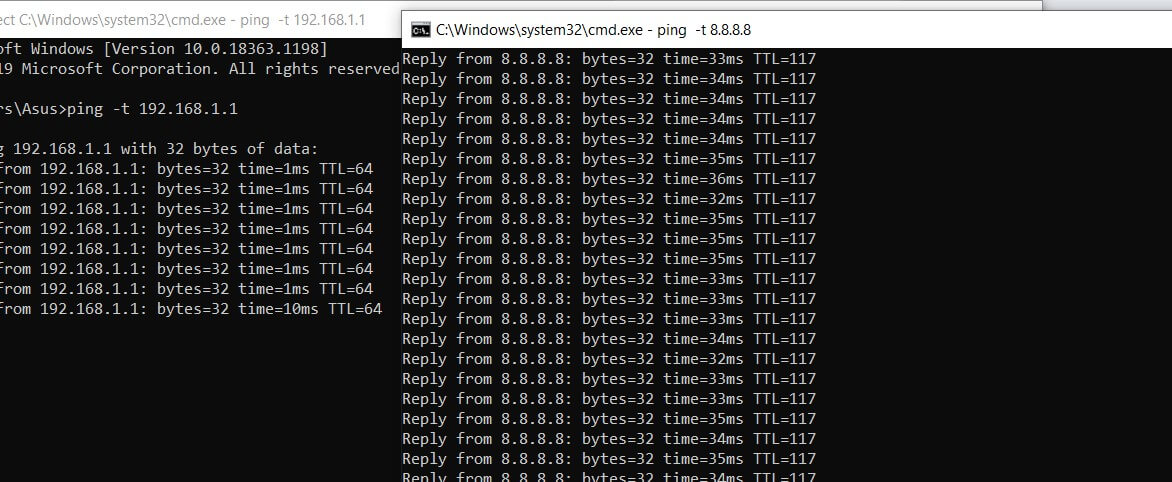
In the case of a DNS from another provider, even if queried by its network, the latency is already higher:
The Google DNS is also invulnerable to attacks cache poisoning that aims to alter the cache’s contents to provide altered responses to questions from the client systems and type attacks Denial of Service (DoS).
The Google DNS protocols have embraced DNS-over-HTTPS and DNS-over-TLS (DoH and DoT respectively) that allow, at the user’s request or the client in use, to encrypt the resolution of domain name requests.
As we explained in the article DNS Google updated to support DNS-over-TLS and encrypt data; for example, by visiting an HTTPS site, the data traffic flows to and from the remote ServerServer in encrypted form without anyone being able to read and monitor it (they cannot possible MITM attacks, man-in-the-middle ).
However, typical DNS requests are handled in the exact text so the Internet provider, users connected to the same local network and other subjects along the way, can quickly establish – in real-time – the websites visited.
The use of the DNS-over-TLS and DNS-over-HTTPS protocols allows overcoming this problem by appropriately encrypting the traffic to and from the DNS servers (not all DNS servers are compatible; Google DNS are).
On mobile devices, for now, only Android nine and later allow you to send requests using DNS packet encryption: access the operating system network settings, choose Advanced, Private DNSthen set dns.google as the service provider.
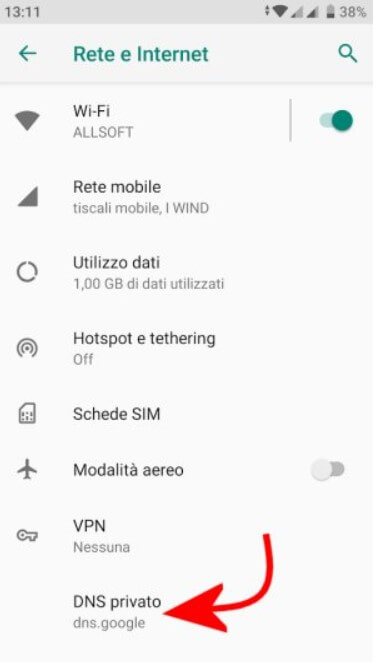
As Google notes on this support page, the private DNS setting and, therefore, the use of the DNS-over-TLS protocol are ignored if a VPN service is used.
Linux users can use the Stubby resolver, while Windows users can orient themselves on Simple DNSCrypt . Unfortunately, not even Windows 10 supports, at the moment and by default, the DNS-over-TLS protocol.
However, Windows will soon support the DNS-over-HTTPS protocol, in line with what has been done by the developers of the leading web browsers.
Unlike what happens above all in Italy, moreover, Google DNS – like those of the other providers mentioned in this article – do not redirect the user to arbitrary web pages following requests for resolution of non-existent domain names (some Internet providers, when a query fails, they send the browser to a “custom page” that shows links and banner ads).
What are Google DNS and how to set them on the router: IPv4 and IPv6 addresses
To set the Google DNS at the router level, connect to its administration panel (usually by typing http://192.168.1.1 or http://192.168.0.1 in the browser address bar), access the LAN section, LAN settings, or Internet configuration depending on the models, then type 8.8.8.8 and 8.8.4.4 in the boxes relating to the primary and secondary DNS servers to use.
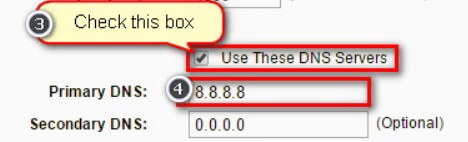
From now on, all clients connected to the local network that asks for a private IP and the DNS servers to use will automatically receive those from Google.
If you were connected with an Internet provider that has already activated an IPv6 network, you could use – also, or – the IPv6 addresses of the Google DNS :
2001: 4860: 4860 :: 8888
2001: 4860: 4860 :: 8844
All the leading operating systems have been fully compatible, for some time, with IPv6 addressing. Simultaneously, the telecommunications operators have not yet adapted their networks (yes, they can perform this test to verify it).
Some devices require the direct entry of all eight octets that make up an IPv6 address. In this case, the following form must be used to enter the Google DNS:
2001: 4860: 4860: 0: 0: 0: 0: 8888
2001: 4860: 4860: 0: 0: 0: 0: 8844
To find out more about IPv6 can be referred to in articles IPv6. What is it and why is it essential in optical Internet of Things.
By consulting this page it is possible to perform a test to understand whether or not you were on an IPv6 network (all the most current operating systems have been IPv6 compatible for some time).
The provision of an IPv6 address by TIM to the connected modem router is, for the moment, still experimental (it is defined as a “pilot solution”: here more information in the IPv6 Protocol section ).
Use Google DNS in Windows and other operating systems
To use Google DNS at the single Windows machine level, press the Windows + R key combination and type ncpa.cpl or, in any case, refer to the Network and Sharing Center.
By right-clicking on the network interface in use, choosing Properties, then Internet Protocol version 4 and Internet Protocol version 6, and finally clicking on the Properties button again, you can set the Google IPv4 DNS (8.8.8.8 and 8.8.4.4) and IPv6 (2001: 4860: 4860:: 8888 and 2001: 4860: 4860:: 8844) in the Use the following DNS server addresses fields.
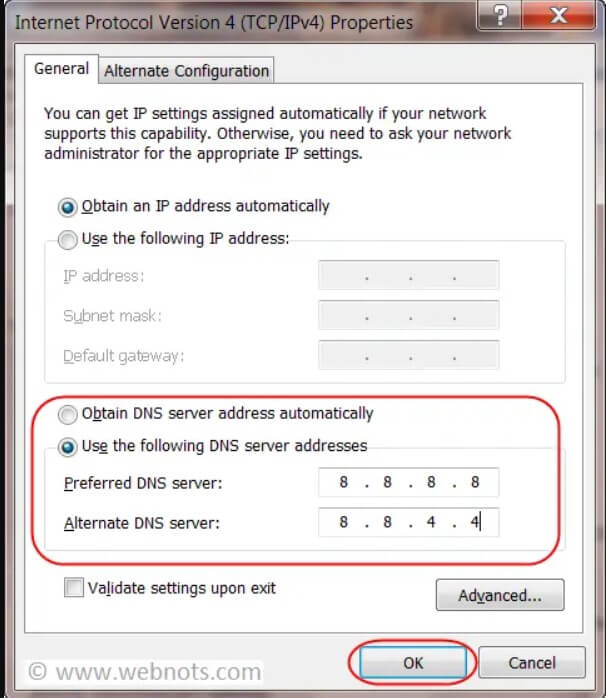
Starting with the Windows 10 May 2019 Update (version 1903), you can change the DNS in use on your machine even faster by typing Network Status in the operating system search box and then clicking Change Connection Properties.
To get instructions on how to change DNS and use Google DNS with other operating systems (Linux, macOS, Android, etc.), we recommend that you refer to our article Change DNS in Windows, Linux macOS, and Android.
Use of Google DNS and privacy
When the Google DNS was launched, many turned up their noses: the Mountain View company has in hand all the technical tools to memorize the list of websites visited by users and, by crossing the data with the Google accounts online, build a profile well precise of each user.
In reality, this type of data crossing is not permissible, and Google undertakes not to keep any information that allows users to be identified.
Google explains that it maintains two logs as part of the DNS service: one temporary and permanent.
The Google DNStemporarily store the IP of the machine from which you are connected. This is useful information to unmask and block any DDoS ( Distributed Denial of Service ) attacks in the bud and solve non-viewing websites concerning a small circle of users.
These temporary logs are deleted within a period of between 24 and 48 hours.
In the permanent logs, Google does not record any information that makes each user uniquely identifiable or the users’ IPs.
Google keeps some geographic information to analyze phenomena and trends, but the records are reset within two weeks (the company supports only a small subset, selected at random).
Google ensures that it does not correlate any information taken from temporary and/or permanent logs with any other data provided to the company in the context of the use of other services (i.e., Google account, Gmail, Photos, …).
Query Google DNS from web or apps
Functionality little known to most, Google provides a control panel and APIs that return the parameters related to a domain name’s resolution.
By connecting to the dns.google page, you can type in any domain name and obtain the IPs used by the corresponding website in Response.
The result is the same as that obtainable with the nslookup command.
By typing in a public IP address, it is also possible to perform a reverse DNS.
Using the syntax https://dns.google.com/resolve?name=google.it you get an output in JSON format while usinghttps://dns.google.com/query?name=google.it a more humanly readable answer.
Always check the DNS servers in use
Without even accessing the router configuration panel, the F-Secure Router Checker service (click on Check router ) allows you to “estimate” the DNS servers in use by the machine or device you are using. At the end of the test, you can click on View the results in detail.
However, it is always worth checking the configuration of the DNS servers on the modem router side and remember to update the device firmware.
It has happened several times that attackers have exploited vulnerabilities in the router to modify the DNS servers configured by replacing them with malicious servers (thus activating the resolution of known domain names on malicious web servers, designed to mislead the user and steal his credentials access).
What does “Response from a non-authoritative server” mean, and what authoritative DNS servers are
In most cases, typing nslookup followed by the domain name to check will result in Response from a non-authoritative server.
This is a standard message which indicates that the domain resolution was performed by a “common” DNS server, not by the authoritative one.
Each Internet domain is based on an authoritative DNS that “has the powers” to communicate to all the others, which is the correct IP associated with the mnemonic address corresponding to the domain name itself.
Whoever manages a website with its domain name knows very well that when you change provider (i.e., hosting service provider), it is necessary to instruct the DNS server to associate the new IP address on which the webserver is listening.
The change, once the authoritative DNS for the domain has been correctly set, must then automatically “propagate” to all DNS servers worldwide.
Using a WHOIS service like this, you can find the authoritative DNS servers for any domain.
Just type in the mnemonic address of interest, then scroll down to Nameservers.
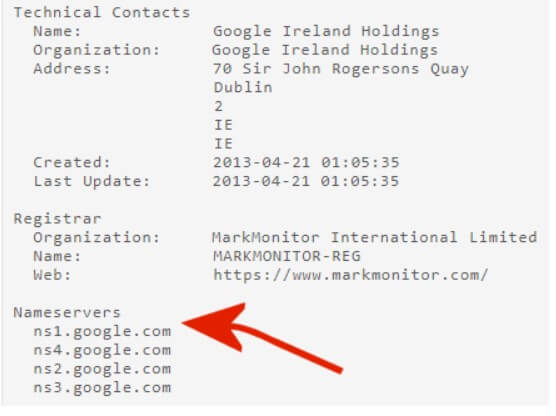
In the case of google.it, for example, the authoritative servers are those indicated with the red arrow.
In fact, by typing nslookup www.google.it ns1.google.com , the message Reply from a non-authoritative server no longer appears.
Larger websites that boast heavy traffic use a load balancing scheme. The authoritative DNS, that is, provide different IP addresses that point to other machines within the same infrastructure (local or distributed) to sort the connection requests of the client systems in a reasonably homogeneous way. This approach helps to avoid any congestion or overloading of web servers.
Finally, an impressive trick for those waiting to propagate new DNS records after a significant change. If Google does not update its DNS records and responds with messages such as ServerServer failed or with ” Name servers refused query (lame delegation?) ” At the address dns.google , then just go to the Flush cache for a domain page, type the domain name of interest and click on Flush cache.

I’m Mr.Love . I’m admin of Techsmartest.com